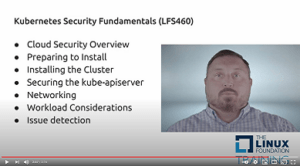
Use hands-on labs to learn new skills and knowledge across a range of security best practices for container-based applications & Kubernetes platforms that will make your IT career profile stand out. In this course you learn to maintain security in dynamic, multi-project environments & address security concerns for cloud production environments.
In this live, instructor-led course you will learn with a cohort of fellow IT professionals while gaining key knowledge & skills related to the Certified Kubernetes Security Specialist (CKS) certification exam. Course enrollment includes:
→ FREE CKS exam registration: 12 months to schedule with one retake
→ FREE CKS exam simulator: 2 attempts
→ 12-month access to course materials